How to Block Personal USB Drives and Allow Company USB Drives Using Microsoft Intune
In today’s hybrid work environment, controlling USB drive
usage is critical to prevent data leaks, malware infections, and compliance
violations. Personal USB devices pose significant risks, while company-issued
drives are often encrypted and monitored. Microsoft Intune provides a
streamlined way to enforce this control. This guide explains why
restricting USB access matters, how to configure Intune policies to
block personal drives, and best practices for seamless
implementation.
Why Restrict Personal USB Drives?
- Data
Security Risks
- Compliance
Requirements
- Device
Management
- Operational
Consistency
Step-by-Step Guide to Block Personal USBs
- Select Attack Surface Reduction
- Select Reusable Settings and click on Add
- Once added, a configure reusable setting box will appear; enter the correct name to identify the setting
- Under Configuration Settings click Add
- Then click select then Removable Storage
- Once added, it displays the configure setting; click it.
- This option can be used if you need to block any USB drives Enter only Name primary ID
- Name: Any Removable Media
- PrimaryID: RemovableMediaDevices
Once it has been added, click "Save."
- Once configured, the device controller pane with the Any Removable device can be shown below.
- For Match Type select Match Any
- After that, users must enable the company ÜSB Drive before we configure the reusable settings again. "Allow Comany Pen Drive" then click to Next
Once you click "Next," then click add removable storage will be displayed. Click to add, then select "Show Configuration Settings."
- After that, you can see what's different option , but in the present situation, we used the serial number option to create the name Identify and allow pen list.
- You can view and modify a specific configuration setting name.
- You can add many entries for additional USB devices identified by serial number or create an entry to allow USB devices from a specific manufacturer
- After defining the two reusable settings, Block personal All Sub Drive
- Click on Create Policy
- In the Create a Profile pop-up window select Platform as Windows 10, Windows 11,
- In Profile select Device Control
- Click Create
- Give the policy's name and description (if applicable).
- Click Next
- In the next window scroll down and go to Device Control
- Click to Add
- provide a policy name.
- Click on Set Reusable Setting under Included ID and Excluded ID one by one
- Add the block all USB Mas storage policy created in earlier under Included ID and Add the Approved USB Mass Storage policy created in earlier under Excluded ID
- Save
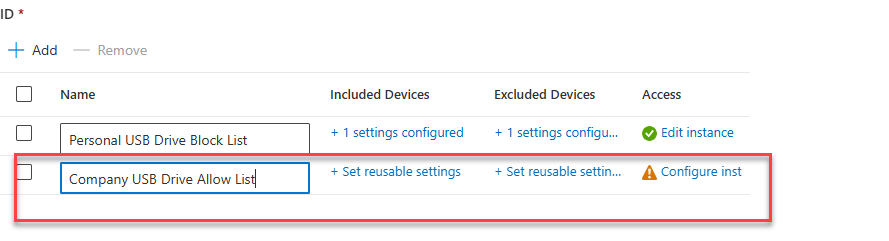
- The policy should look like this if configured correctly
- Include Device - block personal device
- Excluded Device - Allow Company pen drive
- Enter the policy name like "Personal USB Block List - USB Access "
- Expand Device Control in the setup options and make all or just one or two entries in order to secure your origination.
Enter the policy name like "Company USB Drive Allow List - USB Access "
Expand Device Control in the setup options and make all or just one or two entries in order to secure your origination.
- Enter the policy name like "Company USB Drive Allow List - USB Access "
- Expand Device Control in the setup options and make all or just one or two entries in order to secure your origination.
- You must include the devices add allow list in this configuration without using the exclude setting.
- Click to Next .
- Additionally, this explains how to classify groups in order to implement the policy that was defined. Go to the group pane on the left side of the Intune admin center, establish a group, give it a suitable name, and add members (device) if you needs one.
- Assign the proper Device group to the Device Control policy. Next
- The policy appears with attack surface reduction policies.
- Users who plug in a USB drive Personal USB Drive that is not in the approved/ but plug company USB Drive used allowed list it can assessable